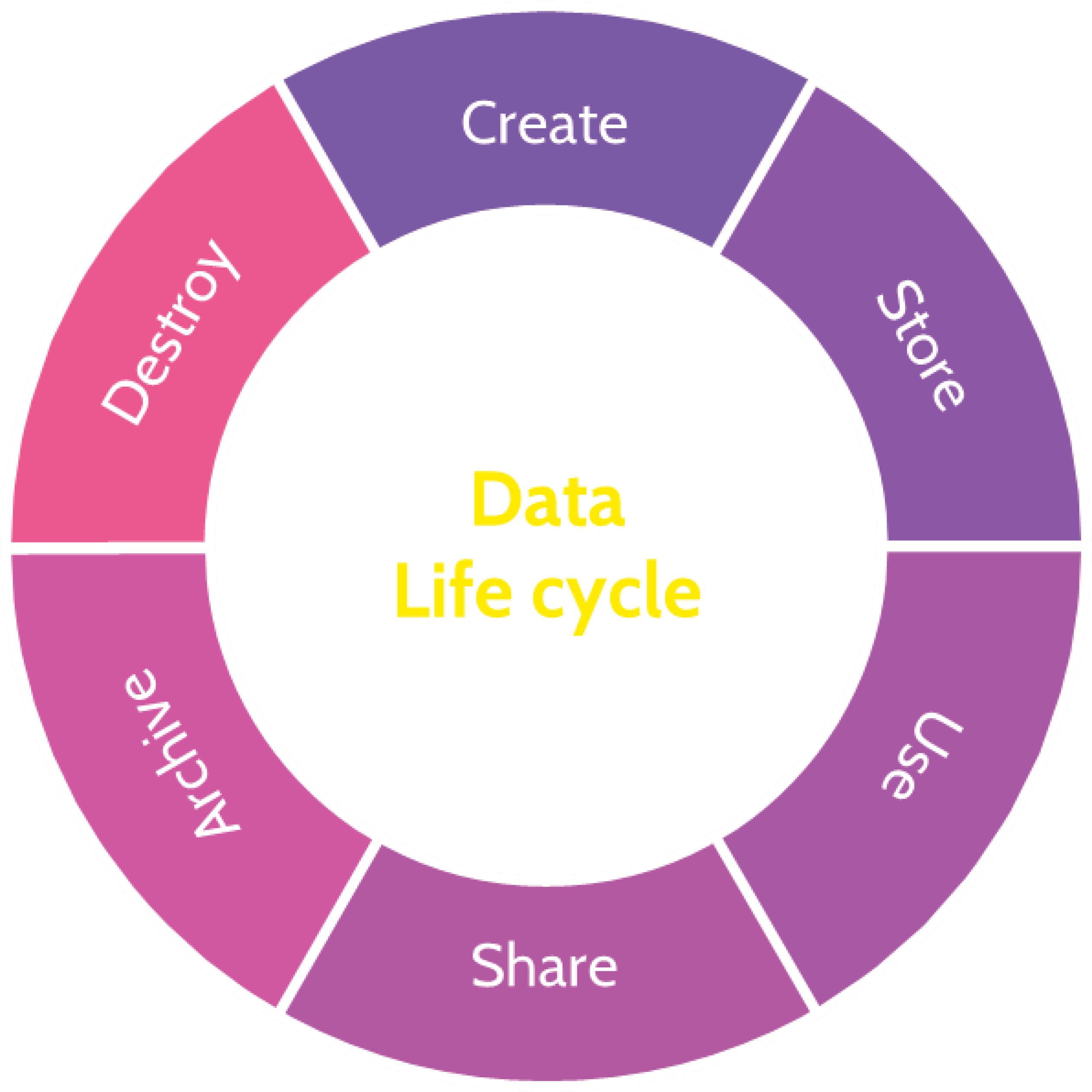
The data lifecycle is a set of six difference phases:
- Create
- Store
- Use
- Share
- Archive
- Destroy
Each of these phases has different requirements in terms of both functionality and security. As an example, when we store sensitive data, we want it to be safely encrypted. But if we kept it encrypted during use, it would have limited utility. It’s our responsibility to understand each of these phases and ensure that data is secured appropriately throughout its entire lifecycle, not just in certain phases. Let’s jump in and take a look at each phase.
Create
Creation is when data is first generated, but updating and modifying existing data can also be considered part of the creation phase. Simple examples of data in the creation phase include writing a Word document or updating a database.
When data is created, it’s important for it to be classified, either manually or automatically. Classification allows us to easily determine the value of data, and the protection mechanisms that we need to put in place to keep it secure. Classification levels can indicate things like how it needs to be encrypted, who can access the data, as well as the purposes that it can be used for.
Store
The data that we create needs to be stored somewhere, so the data storage phase normally takes place alongside creation. Some of the security controls we implement during storage include encryption and access controls that prevent unauthorized parties from accessing it. For the storage phase, we also need to think about availability, as well as backups and recovery. If the data is mission critical, it needs to be stored in a way that is readily accessible, and we must make sure that we have appropriate business continuity and disaster recovery plans in place.
Use
The use phase involves activities like viewing or processing the data. When data is modified through use it is updated, which essentially takes us back to the create phase. The updated data will also need to be stored. Data can be used in a wide variety of ways, so there are many potential security measures we may need to implement during this phase, including things like securing the applications that access the data, implementing data loss prevention, and ensuring appropriate logging is in place.
Share
During the share phase, data is exchanged between users, customers and partners. We want to ensure that data is only shared with authorized parties, and only in appropriate ways that comply with our regulatory requirements.
Archive
At some stage, we may no longer actively need our data, but may still need to keep it around. When this happens, we will often archive our data. One reason we archive data is because of retention requirements that set out how long we are legally required to keep certain types of data. Another reason is because the data may still have value, and we don’t just want to throw it away.
For archiving, we often use long-term storage options like Amazon S3 Glacier. These services can be far cheaper than normal storage options, so we can save substantial amounts of money by archiving data that we no longer actively use. However, these services tend to be slow, which means that it can take a significant amount of time to retrieve data when it is needed. When we archive data, we use similar security controls to those implemented in the store phase.
Destroy
When we no longer need our data, it should be destroyed. In on-premises environments, the destroy phase often involves physically destroying the hardware, using techniques such as incineration or pulverization. In the cloud, we generally use cryptoshredding, which essentially involves encrypting the data with a secure algorithm and throwing away the key.

