CISM Domain 1 - Importance of Information Security Governance MindMap
Download FREE Audio Files and Printable PDFs of our MindMaps
Your information will remain 100% private. Unsubscribe with 1 click.
Transcript
Introduction
Hey, I’m Nick from Destination Certification, and I’m here to help YOU pass the CISM exam.
In this video, we’re going to break down a full MindMap of some of the most important concepts in Information Security Governance from Domain 1— not just to help you memorize terms, but to really understand how they interconnect and why they matter.
Importance of Information Security Governance
Let me say at the outset: this may seem kinda boring. Few people get excited about governance, let alone security governance, but what I’m going to cover here is critically important to understand for the CISM exam, and to be a competent security professional.
You must have the right mindset - you must understand what a well-run security function must always focus on, and what you as a security leader must always focus on.
With that in mind, information security governance establishes the framework that ensures security initiatives support business objectives while protecting organizational assets. It bridges the gap between technical security controls and strategic business decisions, creating accountability structures that make security everyone's responsibility.
Corporate Governance
A central aspect here is corporate governance. It provides the overarching structure through which organizations direct and control their operations. This framework establishes accountability mechanisms, decision-making processes, and oversight responsibilities that ensure the organization operates ethically and achieves its strategic objectives. Think of corporate governance as the GPS of an organization. Without it, you don’t just take wrong turns, you end up explaining to shareholders why you’re parked in a ditch.
Security Governance
Similarly, security governance extends corporate governance principles specifically to information protection, establishing policies, procedures, and accountability structures. It ensures security decisions align with business strategy while maintaining appropriate risk levels and regulatory compliance throughout the organization.
Focus of Security
Let us now begin to break down these forms of governance, starting with a focus on security.
Modern security focus has shifted from purely protective measures to enabling business operations safely. Organizations now view security as a strategic capability that supports innovation, customer trust, and competitive advantage rather than simply preventing breaches. For these reasons, it is essential to focus on security.
Business enablement
Now, when you think about it a bit more, focusing on security sounds a bit abstract,doesn’t it? How exactly are we going to achieve that? One way is through business enablement. Business enablement represents security's evolution from a barrier to a catalyst for organizational success. When security teams understand business objectives and design controls that support rather than hinder operations, they enable new ventures, partnerships, and digital transformations. In other words, it turns security from a cost center into the friend who insists on seatbelts - annoying at first, but the only reason everyone makes it to the party
Value creation
Another way we can focus on security meaningfully is through value creation. Value creation occurs when security investments directly support revenue generation, cost reduction, or risk mitigation that preserves shareholder value during incidents.
Non-obstructive security
Next off, non-obstructive security integrates protection seamlessly into business processes without creating unnecessary friction or delays. This philosophy recognizes that overly restrictive controls drive shadow IT and workarounds that actually increase risk. Successful implementation requires understanding user workflows, automating security decisions where possible, and designing controls that operate transparently in the background. The goal is making the secure path the easiest path for users to follow.
Security Alignment
So how do we achieve this? How do we make security an enabler of the business? An important point here is security alignment. Security allignment ensures protection strategies directly support business objectives and risk tolerance. How exactly do we achieve this very broad goal? We can start from a board-driven tone.
Board-driven tone
Board-driven tone establishes security as a strategic priority through visible leadership commitment and accountability.
Security as enabler
Similarly, security functions as an enabler when it provides the confidence and capabilities for organizations to pursue digital initiatives safely. Rather than saying 'no,' security teams offer secure alternatives that achieve business goals while managing risks appropriately.
Now that we understand the theoretical role security should have, let’s discuss some basic pillars related to security.
Five Pillars of Information Security
The five pillars provide a comprehensive framework for protecting information assets. You think that understanding Confidentiality, Integrity, Availability, Authenticity and Non-repudiation is too easy? I hope you do, as we’ll be starting with another concept – the CIA triad.
CIA Triad
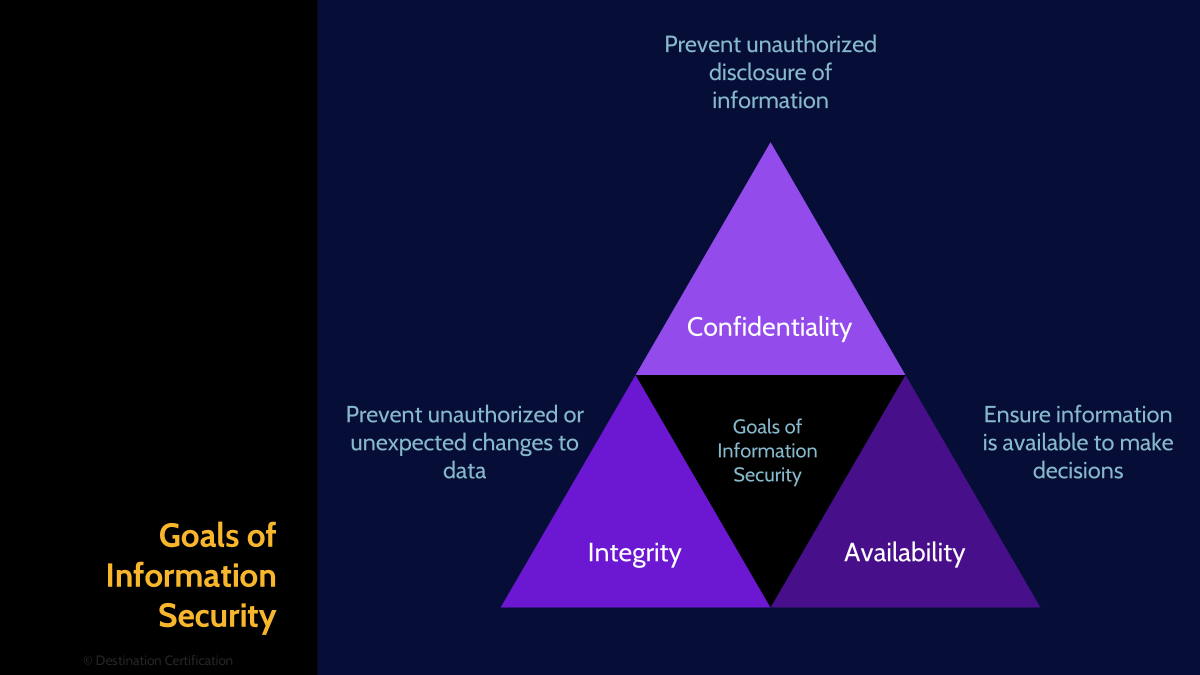
To understand the significance of the five pillars, it helps to start with their roots in the CIA Triad. Confidentiality restricts access, integrity ensures accuracy, and availability guarantees accessibility when needed. Let’s break that up a bit more, starting with confidentiality:
Confidentiality
Confidentiality ensures information is accessible only to authorized individuals, protecting sensitive data from unauthorized disclosure through encryption, access controls, and data classification schemes.
Integrity
Secondly, integrity guarantees data remains accurate and unaltered during storage and transmission, using checksums, digital signatures, and version control to detect and prevent unauthorized modifications.
Availability
Wrapping up the CIA triad, availability ensures authorized users can access information and resources when needed, implementing redundancy, backup systems, and disaster recovery plans to maintain operations. Let’s move on from the CIA triad and ensure we also cover authenticity and non-repuditation.
Authenticity
Authenticity verifies that data, transactions, and communications are genuine and come from verified sources, using digital certificates and authentication mechanisms to establish trust.
Non-repudiation
Non-repudiation prevents parties from denying their actions, creating undeniable proof of data origin, receipt, and transactions through digital signatures and audit logs.
IT security vs Information Security

Thankfully, we’ve made it past CIA and other three-letter acronyms that sound like spy agencies, and can shift our focus from the nuts-and-bolts of IT security to the bigger picture of information security. Understanding the distinction between IT security and information security helps organizations allocate resources appropriately. While IT security focuses on protecting technology infrastructure, information security takes a broader view encompassing all forms of valuable data regardless of format.
IT Security
IT security protects technology infrastructure including servers, networks, and applications, ensuring these digital resources maintain confidentiality, integrity, and availability.
Information Security
Information security encompasses protection of all organizational data whether digital, physical, or intellectual. This broader scope includes paper documents, verbal communications, and knowledge assets, applying CIA principles across all information formats throughout their lifecycle.
Security Governance Outcomes

All of these distinctions and frameworks ultimately lead to one question: how do we prove security is working? The answer lies in governance that delivers outcomes stakeholders can see and measure.
Effective security governance produces measurable outcomes that demonstrate value to stakeholders. There are several important outcomes, starting with strategic alignment.
Strategic Alignment
Strategic alignment ensures security initiatives directly support business goals rather than operating in isolation. This requires security leaders to understand corporate strategy, participate in planning processes, and design programs that enable rather than constrain business growth.
Risk Management
Risk management is highly important and we’ll cover it in a separate MindMap in Domain 2. So, we can move on to discussing value delivery and you can expect to hear a lot more about this later!
Value Delivery
As I said, risk management will be its own separate MindMap so moving on to value delivery - it ensures security investments produce expected benefits, optimizing security spending to maximize risk reduction while minimizing operational impact and resource consumption.
Resource Optimization
Furthermore, resource optimization balances security needs against available budget, personnel, and technology constraints.
Performance Measurement
Next, performance measurement tracks security program effectiveness through meaningful metrics and key performance indicators. These measurements demonstrate security value to executives, identify improvement opportunities, and ensure controls operate as intended to reduce actual risk.
Assurance Process Integration
To wrap up the security governance outcomes, assurance process integration embeds verification activities throughout security operations rather than treating them as separate functions. Think of it as quality control with a pulse, catching issues before they become headlines

And that is an overview of the Importance of Information Security Governance within Domain 1, covering the most critical concepts you need to know for the exam.
Something really cool we are providing with these MindMap videos is a completely FREE downloadable version of all the MindMaps in PDF format. We even include a blank version of each MindMap in case you want to print them out and take notes as you listen along. Link to download the MindMaps is in the description below.
If you found this video helpful you can hit the thumbs up button and if you want to be notified when we release additional videos in this MindMap series, then please subscribe and hit the bell icon to get notifications.
I will provide links to the other MindMap videos in the description below.
Thanks very much for watching! And all the best in your studies


