CISM Domain 1 - Strategic Planning MindMap
Download FREE Audio Files and Printable PDFs of our MindMaps
Your information will remain 100% private. Unsubscribe with 1 click.
Transcript
Introduction
Hey, I’m Nick from Destination Certification, and I’m here to help YOU pass the CISM exam.
In this video, we’re going to break down a full MindMap of some of the most important concepts related to Strategic Planning from Domain 1— not just to help you memorize terms, but to really understand how they interconnect and why they matter.
Business case
Strategic planning sets the destination, and a business case explains why security deserves a seat on that bus. It turns tech jargon into a story executives actually want to fund.
A business case serves as your formal justification for security investments, translating technical requirements into language that resonates with executive decision-makers.
Business case components
Let’s review these main business case components!
Exec summary
Starting with the executive summary.
Your executive summary captures the essence of your entire proposal in a single page, providing busy executives with immediate insight into the value proposition.
Problem statement
Crafting an effective problem statement requires you to articulate not just what's wrong, but why it matters to the business and what happens if nothing changes. The best problem statements quantify risk exposure, identify specific vulnerabilities, and connect security gaps to potential business impacts like revenue loss, regulatory penalties, or reputational damage. This is your burning platform for change — the fire alarm that makes everyone drop their coffee and pay attention.
Solution description
Your solution description transforms abstract security concepts into tangible business outcomes by detailing how proposed controls, technologies, or processes will address identified problems. Rather than focusing solely on technical specifications, effective solution descriptions emphasize operational improvements, risk reduction metrics, and alignment with existing business processes.
Cost-benefit analysis
Cost-benefit analysis represents the financial heart of your business case, requiring sophisticated modeling of both tangible and intangible factors across multiple time horizons. Beyond simple ROI calculations, you must account for risk reduction value, opportunity costs, total cost of ownership including hidden expenses like training and maintenance, and the strategic value of enhanced security posture.
Risk assessment
Risk assessment within your business case identifies potential obstacles to implementation success, from technical challenges to organizational resistance. By proactively addressing these concerns and proposing mitigation strategies, you demonstrate thorough planning and increase stakeholder confidence in your proposal.
Implementation plan
A robust implementation plan breaks down your security initiative into manageable phases with clear milestones, resource requirements, and success criteria for each stage. This roadmap demonstrates feasibility by showing exactly how you'll transition from current state to desired state, including dependencies, critical path activities, and contingency plans for common obstacles. Stakeholders want proof you’ve thought past the shiny pitch — down to who’s installing it, who’s grumbling about the change, and how it actually works on Monday morning.
Recommendations
Recommendations crystallize your analysis into specific, actionable next steps that decision-makers can approve and implement.
Budget
Once the core components of the business case are in place, the next question is inevitable: how much will it cost? That’s where the budget section comes in.
The budget section details all financial requirements including capital expenditures, operational costs, and resource allocations necessary for successful implementation.
Workforce composition and key skills

You can buy all the tools in the world, but without the right people to run them, security is just shelfware. That’s why workforce skills matter.
Understanding workforce composition and key skills enables strategic alignment between security capabilities and human capital investments.
Technical proficiency
With that in mind, technical proficiency in security extends far beyond basic tool operation, encompassing deep understanding of system architectures, threat vectors, and defensive strategies across multiple technology domains. Today's security professionals must navigate complex hybrid environments, understand cloud-native security models, and adapt traditional controls to emerging technologies like containerization and serverless computing.
Communication
Next off, effective communication bridges the gap between technical security teams and business stakeholders, translating complex threats into understandable risks and actionable recommendations.
Analytical thinking
Similarly, analytical thinking in security contexts involves decomposing complex problems into manageable components, identifying patterns across seemingly unrelated events, and synthesizing diverse data sources to form coherent threat pictures.
Leadership
Security leadership involves guiding teams through crisis situations, building security-conscious cultures, and influencing organizational behavior without formal authority. The best leaders are part tech guru, part therapist, and part diplomat — building trust while getting the job done.
SWOT Analysis

Once you understand your team’s skills and capabilities, the next step is to put them in context. SWOT analysis provides the framework to evaluate strengths, weaknesses, opportunities, and threats across the program. Let’s go through these:
Strengths
Strengths represent internal capabilities, resources, or advantages that enhance your security posture and provide competitive differentiation in the marketplace.
Weaknesses
Weaknesses identify internal limitations, resource constraints, or capability gaps that could be exploited by adversaries or hinder security program effectiveness. Honest assessment of weaknesses enables targeted improvements and risk mitigation strategies that strengthen overall security posture.
Opportunities
Opportunities emerge from external trends, technological advances, or market conditions that could enhance your security program's effectiveness or efficiency. Opportunities might look like shiny new security tech, regulators suddenly footing a bigger part of the bill, or teaming up with partners who make your defenses stronger.
Threats
Threats encompass external factors including adversary capabilities, emerging attack vectors, and environmental changes that could compromise your security posture.
Security Program Metrics
A SWOT analysis tells you where you stand, but metrics tell you if you’re actually moving. They put hard numbers on performance, risk, and value and they’re the next piece we’ll be reviewing.
Security program metrics provide quantitative measures of performance, risk, and value delivery that enable data-driven decision making and continuous improvement.
KPI
Key Performance Indicators measure operational efficiency and effectiveness of security controls, processes, and teams against established baselines and targets. The main types of these include strategic, operational and tactical. Let’s review these!
Strategic
Strategic KPIs align security performance with long-term organizational objectives, measuring how effectively security investments support business growth, risk appetite, and competitive positioning. These metrics typically span multiple quarters or years, tracking trends in security maturity, risk reduction, and value creation. Examples include security investment ROI, time to detect advanced threats, and security's contribution to business enablement initiatives.
Operational
Operational KPIs track day-to-day security activities and process performance, such as patch compliance rates, incident response times, and vulnerability remediation speeds.
Tactical
Tactical KPIs measure immediate security activities and control effectiveness, including firewall block rates, malware detection counts, and user training completion percentages.
KGI
KPIs tell you how well you’re rowing, but KGIs tell you if you’re actually getting to shore.
Key Goal Indicators measure achievement of strategic objectives, showing whether security initiatives deliver intended business outcomes and value.
CSF
Apologies for the alphabet soup — KPIs, KGIs, and now one more. But CSFs are worth it: they spotlight the must-haves your security program needs to succeed.
Critical Success Factors identify essential conditions or capabilities that must exist for security programs to achieve their strategic objectives.
KRI criteria
While Critical Success Factors define what must go right, organizations also need a way to watch for what could go wrong. That’s the role of Key Risk Indicators.
Key Risk Indicator criteria establish thresholds and parameters for identifying emerging risks before they materialize into incidents. Think of KRIs as early warning sirens: they spot trouble in the trends so you can fix problems before they blow up into full-blown incidents.
Impact
Impact measures the potential business consequences if a risk materializes, typically quantified in financial terms, operational disruption, or reputational damage.
Effort
Effort quantifies resources required to implement and maintain security controls, including time, money, personnel, and opportunity costs.
Reliability
Reliability in metrics ensures consistent, reproducible measurements across time periods and different evaluators. Reliable metrics maintain their accuracy regardless of who collects the data or when measurements occur, providing stable baselines for trend analysis and decision-making.
Sensitivity
Our last KRI criteria is sensitivity. It determines how quickly metrics respond to changes in underlying conditions, balancing between excessive noise from minor fluctuations and delayed detection of significant trends. Well-calibrated sensitivity enables timely identification of emerging issues without triggering false alarms from normal variations.
Effective Metrics
KRIs highlight emerging risks, but they’re only part of the bigger picture. Effective metrics integrate these insights into a clear view of performance and risk that leaders can act on
Effective metrics drive meaningful action by providing clear insights into security performance and risk posture. The goal is simple: give leaders clarity at a glance, not a 200-page bedtime story in disguise.
Accurate
To start us off, accurate metrics play a pivotal role in ensuring that decision-making is grounded in reliable evidence.
Cost-effective
Secondly, cost-effective metrics deliver valuable insights without excessive collection or analysis expenses.
Repeatable
Next, repeatable metrics follow standardized collection and calculation procedures that produce consistent results across different time periods and evaluators.
Predictive
Moving on, predictive metrics identify emerging trends before they become problems, enabling proactive intervention and risk mitigation.
Actionable
Actionable metrics provide clear guidance on required responses, linking measurements directly to specific improvement activities or risk mitigation steps.
Managable
Building on this, manageable metrics are those that remain practical to track and act upon, staying within the team’s capacity while still delivering meaningful value.
Meaningful
In addition, meaningful metrics directly reflect progress toward core goals, ensuring the data collected provides genuine insight rather than superficial numbers.
Unambigious
Similarly, unambiguous metrics are clearly defined and interpreted in only one way, eliminating confusion and ensuring consistent understanding across all stakeholders.
Genuine
Finally, genuine metrics accurately represent the reality they are intended to measure, avoiding distortion or manipulation that could mislead decision-making.
Risk management Framework
It’s great to show keeping tracks and creates value, but stakeholders also ask: what about the risks? Risk management answers by balancing threats, costs, and impact.
A Risk Management Framework provides structured approaches for identifying, assessing, treating, and monitoring risks across the enterprise. More about these in Domain 2, for now, let us move on to risk roles.
Risk Roles
Risk roles define clear responsibilities and accountabilities for risk management activities across the organization. When roles are defined right, you don’t get gaps, overlaps, or turf wars — just a security team that fights threats instead of each other. Let us start of by first reviewing risk owners.
Risk owner
Risk owners hold ultimate accountability for specific risks, making decisions about acceptance, mitigation, or transfer based on business context.
Senior management
Next off, senior management establishes risk appetite, allocates resources for risk management, and ensures that risk considerations inform strategic decisions. Their engagement signals organizational commitment to risk management, influencing culture and behavior throughout the enterprise. Effective senior management involvement requires regular risk reporting that translates technical vulnerabilities into business impacts, enabling informed decision-making about risk acceptance and mitigation investments.
Risk management team
Moving on , the risk management team serves as the organizational nerve center for threat intelligence, risk assessment, and mitigation coordination across diverse business units and technical domains. These professionals must possess a unique blend of technical expertise, business acumen, and communication skills that enable them to translate between technical vulnerabilities and business impacts.
Employees
Next up, employees serve as the first line of defense, identifying and reporting potential risks while following established security policies and procedures.
Documentation
Now, we can define roles and manage risks, but how do we prove we actually did it? That’s where risk documentation comes in
Risk documentation creates institutional memory and audit trails that demonstrate due diligence in risk management. Comprehensive documentation captures risk assessments, treatment decisions, and residual risk acceptance, providing transparency for stakeholders and regulators while enabling knowledge transfer. What does our documentation need to have? Let’s start with objectives.
Objectives
Risk documentation objectives include maintaining compliance evidence, enabling consistent risk treatment, and providing historical context for risk decisions.
Audience
Next off, documentation audiences range from technical teams requiring detailed control specifications to executives needing high-level risk summaries and trend analyses.
Information resources
Furthermore, information resources for risk management encompass internal data sources like vulnerability scans and incident reports, external threat intelligence feeds, industry benchmarks, and regulatory guidance that collectively inform risk assessments. The challenge lies in synthesizing diverse, often conflicting information streams into coherent risk pictures that support decision-making. Organizations must develop capabilities to evaluate source credibility, correlate disparate indicators, and extract actionable intelligence from noise. Effective information resource management also requires understanding the temporal nature of risk data, recognizing when information becomes stale and when real-time feeds are necessary versus periodic assessments.
Assumptions
Risk assumptions document the underlying beliefs and constraints that shape risk assessments and treatment decisions.
Decision criteria
Finally, decision criteria establish consistent thresholds and parameters for risk treatment choices, ensuring similar risks receive comparable responses regardless of who performs the assessment.
Balanced Scorecard
One more big idea before we wrap up — and it’s worth the airtime. The Balanced Scorecard shows how to turn strategy into measurable action across the whole organization.
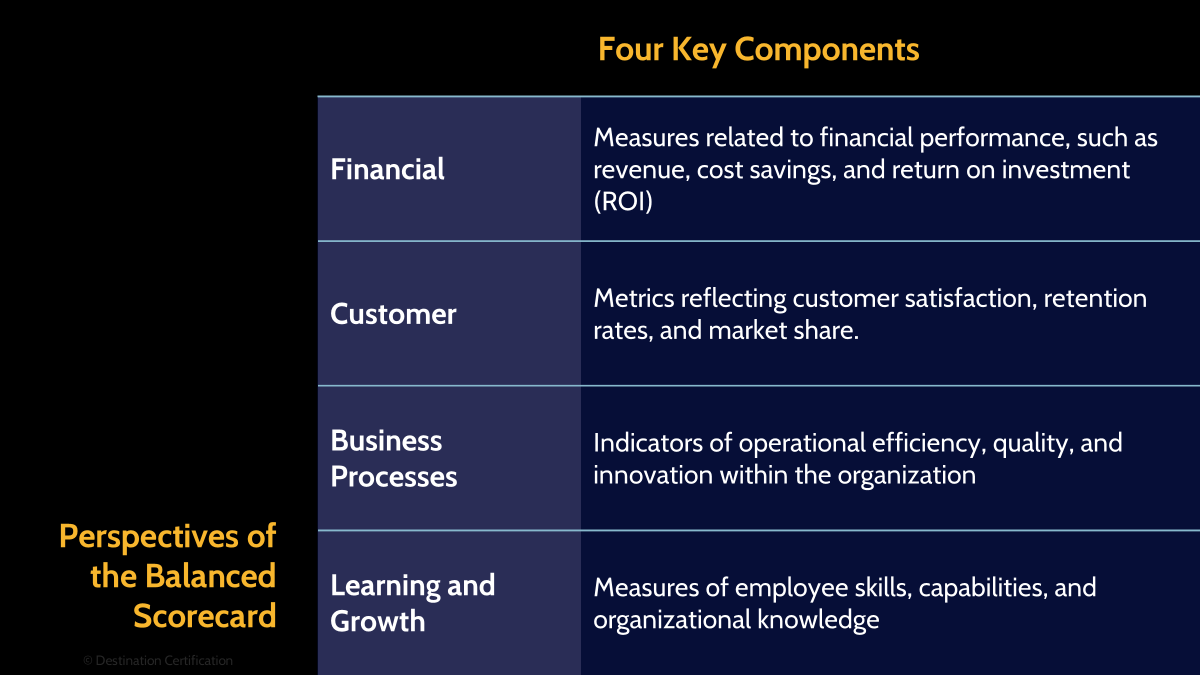
The Balanced Scorecard translates security strategy into operational metrics across multiple perspectives, ensuring comprehensive performance measurement beyond traditional financial indicators.By balancing multiple perspectives, organizations avoid the tunnel vision that comes from focusing solely on technical metrics or financial returns. Of course, these sound like big ideas, so how exactly are they implemented?
Has four main components
Interesting question, very shortly we can say that the four components of the Balanced Scorecard create a holistic view of security program performance by examining different but interconnected dimensions of value creation. These components are Financial, Customer, Business, Process, and Learning and growth. Let us dive into the financial component.
Financial
Firstly, the financial perspective measures security's contribution to organizational financial performance through cost reduction, loss prevention, and efficiency improvements.
Customer
Secondly, the customer perspective evaluates how well security services meet stakeholder needs, measuring satisfaction, trust, and perceived value.
Business Process
Next up, business process metrics examine the efficiency and effectiveness of security operations, from incident response times to vulnerability remediation rates. Think of them as the X-ray for your processes — spotting the bottlenecks, pointing out the shortcuts, and saving money along the way.
Learning and growth
Finally, learning and growth perspectives focus on building future security capabilities through skill development, knowledge management, and innovation initiatives. This forward-looking lens makes sure security doesn’t just stand still, but keeps leveling up to take on the next wave of threats and tech.

And that is an overview of Strategic Planning within Domain 1, covering the most critical concepts you need to know for the exam.
Something really cool we are providing with these MindMap videos is a completely FREE downloadable version of all the MindMaps in PDF format. We even include a blank version of each MindMap in case you want to print them out and take notes as you listen along. Link to download the MindMaps is in the description below.
If you found this video helpful you can hit the thumbs up button and if you want to be notified when we release additional videos in this MindMap series, then please subscribe and hit the bell icon to get notifications.
I will provide links to the other MindMap videos in the description below.
Thanks very much for watching! And all the best in your studies


