CISM Domain 1 - Strategy Development MindMap
Download FREE Audio Files and Printable PDFs of our MindMaps
Your information will remain 100% private. Unsubscribe with 1 click.
Transcript
Introduction
Hey, I’m Nick from Destination Certification, and I’m here to help YOU pass the CISM exam.
In this video, we’re going to break down a full MindMap of some of the most important concepts in Information Security Governance from Domain 1— not just to help you memorize terms, but to really understand how they interconnect and why they matter.
Sets clear goals, policies, and practices to protect information assets effectively.
Strategy development forms the backbone of any successful security program. When we develop security strategies, we're creating a comprehensive framework that aligns security initiatives with business objectives. This process requires careful planning, stakeholder engagement, and a deep understanding of both current capabilities and future needs. The strategy becomes your north star, guiding every security decision and investment your organization makes.
To put this simply, a security strategy translates organizational goals into actionable security initiatives.
Information Security Policies, Procedures Baselines & Guidelines
Is it really that simple? Well, it can be if we break it down: the foundation of any security program rests on well-crafted policies, procedures, baselines, and guidelines. These documents work together as a hierarchical framework where policies set the high-level direction, standards establish specific requirements, procedures detail step-by-step processes, baselines define minimum security configurations, and guidelines offer recommended best practices.
Policies
Policies represent the highest level of security documentation, serving as formal statements of management's intent and commitment to security. They nail down the ‘what’ and ‘why’ of security, leaving the ‘how’ to the folks who actually get their hands on the keyboard. Effective policies are broad enough to remain stable over time yet specific enough to provide clear direction.
Management's goals and objectives.
Documentation and communication of management's security goals serves as the critical link between executive vision and operational reality. This process involves translating strategic objectives into clear, actionable language that resonates with all organizational levels. Clear communication makes security less of a rulebook and more of a rallying point for the whole organization.
Defining security team
Furthermore, we need to define the security team's elements, functions, and scope in a way that establishes clear boundaries and responsibilities within the organization.
AUP (Acceptable Use Policy)

Once the boundaries for security are clear, they need to be translated into rules everyone can understand — starting with the Acceptable Use Policy The Acceptable Use Policy serves as a contract between the organization and its users, establishing clear boundaries for technology resource usage. It addresses everything from email and internet usage to social media conduct and personal device usage. The AUP is mission-critical in today’s world of remote work and BYOD, where personal and professional tech often end up sharing the same coffee shop Wi-Fi.
Specifies permitted uses of IT resources
Firstly, specifying permitted uses of IT resources provides users with clear guidance on appropriate technology usage while supporting business productivity. Instead of just giving yes/no rules, it explains the ‘why’ behind permissions — so when you’re staring at that sketchy coffee shop Wi-Fi, you actually know whether to click ‘Connect’ or not.
Outlines activities that are strictly prohibited
Secondly, outlining prohibited activities protects the organization from legal, financial, and reputational risks while establishing clear red lines for user behavior. These prohibitions typically include illegal activities, harassment, unauthorized access attempts, copyright infringement, and activities that could compromise security or network performance. It’s about saying enough to matter, but not so much that users need a bookmark to get through it.
Clearly defines disciplinary actions
Thirdly, clear definition of disciplinary actions ensures consistent, fair enforcement of security policies across the organization. Just like spilling coffee on your laptop might earn you a warning but walking out with the café’s Wi-Fi router will get you banned, disciplinary measures progress from gentle reminders and training to termination and even legal action for the serious stuff. With that, you can now understand how these nuances of policy can meaningfully impact strategy development.
Standards
Policies set the direction, but they only work if translated into clear expectations. That’s where standards step in. Standards translate policy requirements into specific, measurable criteria that must be met. For example, if policy requires strong authentication, standards specify minimum password length, complexity requirements, and multi-factor authentication implementation.
Procedures
Next, procedures provide the detailed, step-by-step instructions for implementing security controls and responding to security events. They transform standards and policies from abstract requirements into concrete actions that staff can follow. Well-written procedures reduce errors, ensure consistency, and enable rapid response during incidents when stress might otherwise lead to mistakes..
Basslines
Another important aspect is baselines. Baselines establish the minimum security configuration for systems and applications across your environment.
Guidelines
Finally, guidelines offer recommended best practices and suggestions for implementing security in situations where strict requirements may not be appropriate or feasible. Guidelines aren’t handcuffs — they’re guardrails. They give users room to adapt, especially when tech and threats change faster than policies can. The goal is to have smarter choices without slowing down innovation
SMART goals

Of course, even the best policies and standards need a way to measure success. That’s where SMART goals come in. By ensuring goals are Specific, Measurable, Achievable, Relevant, and Timely, security teams can track progress, demonstrate value to stakeholders, and maintain focus on what truly matters for organizational security improvement.
Specific
Specific goals clearly define what will be accomplished, removing ambiguity and ensuring everyone understands the target outcome.
Measurable
Next off, measurable goals include quantifiable metrics that allow you to track progress and definitively determine success. For security, this might mean reducing incidents by a percentage, achieving specific compliance scores, or improving response times to defined thresholds.
Achievable
Achievable goals stretch the team while remaining realistic given available resources, time constraints, and organizational maturity. Setting overly ambitious goals leads to frustration and failure, while goals that are too easy fail to drive meaningful improvement.
Relevant
Relevant goals align with broader organizational objectives and address actual risks rather than theoretical concerns.
Timely
Timely, time-bound, on-time or however you want to call these (as large organizations and international frameworks won’t fully agree on this), here is what you need to know about these goals: timely goals have clear deadlines that create urgency and enable progress tracking against scheduled milestones.
Elements of a Security Strategy
SMART goals set the destination, but you still need the whole map. That’s where a comprehensive security strategy comes in.
A comprehensive security strategy incorporates multiple interconnected elements that work together to create a cohesive security program. These elements provide structure and direction while maintaining flexibility to adapt to changing threats and business needs.
Include a roadmap
A security roadmap visualizes the journey from current state to desired future state, showing major milestones, dependencies, and resource requirements. This visual representation helps stakeholders understand the sequence of initiatives and how individual projects contribute to overall security maturity.
Long-term goals
Long-term goals establish the vision for where security needs to be in three to five years, considering business growth, technology evolution, and threat landscape changes.
Have sub-goals
Sub-goals break large, complex objectives into manageable chunks that can be achieved incrementally. Each sub-goal represents a stepping stone toward the larger objective, allowing teams to maintain momentum through regular achievements while building toward transformational change.
Include metrics
Finally, metrics provide objective evidence of security program effectiveness and progress toward goals. The scoreboard might track how fast you detect incidents, how well systems stick to the baseline, or how many people survive security training without snoozing.
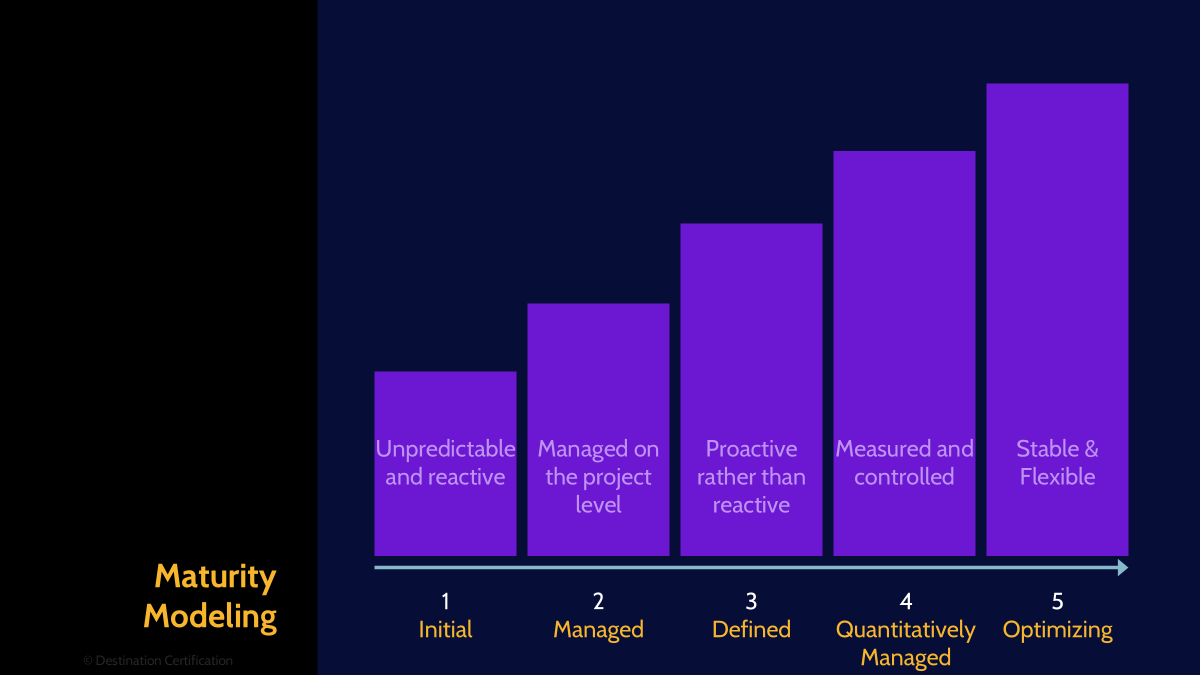
CMMI maturity modelling
I do hope you haven’t snoozed off and have a bit more energy left for one of our last concepts.
The Capability Maturity Model Integration provides a framework for assessing and improving security program maturity through defined evolutionary stages. Each level represents increasing sophistication in how security processes are managed, measured, and optimized. Organizations use CMMI to benchmark their current capabilities, identify gaps, and create roadmaps for systematic improvement. This model helps communicate security maturity to executives in business terms they understand.
Level 0
Level 0 represents complete absence of formal security processes, where no structured approach to security exists.
Level 1
Next up, Level 1 indicates ad-hoc, chaotic processes that depend on individual heroics rather than repeatable practices.
Initial
The Initial stage reflects unpredictable processes where success depends on individual competence rather than organizational capability. It’s basically security by ‘best effort,’ where success depends on who’s at the keyboard that day.
Level 2
Moving on, Level 2 introduces basic project management discipline, ensuring processes are planned and executed according to documented procedures.
Managed
At this stage, managed processes are planned, performed, monitored, and controlled at the project level with established policies.
Level 3
Then, level 3 establishes standard processes across the organization, moving from project-specific to organization-wide consistency.How exactly?
Defined
Through defined processes - these are well-characterized, understood, and described in standards, procedures, tools, and methods across the organization.
Level 4
Level 4 introduces quantitative management where processes are controlled using statistical and quantitative techniques.
Quantitatively Managed
Quantitatively managed processes use metrics and statistical analysis to predict performance and identify variations. Quality and process performance are understood in statistical terms and managed throughout the process lifecycle, enabling data-driven decision making.
Level 5
Finally, Level 5 represents the pinnacle of process maturity where continuous improvement is embedded in organizational culture.
Optimizing
Central to that is optimizing. Optimizing organizations focus on continuous improvement through both incremental and innovative technological improvements. Processes are constantly refined based on quantitative understanding of common causes of variation, with a culture that encourages innovation and proactive problem prevention.

And that is an overview of Strategy Development within Domain 1, covering the most critical concepts you need to know for the exam.
Something really cool we are providing with these MindMap videos is a completely FREE downloadable version of all the MindMaps in PDF format. We even include a blank version of each MindMap in case you want to print them out and take notes as you listen along. Link to download the MindMaps is in the description below.
If you found this video helpful you can hit the thumbs up button and if you want to be notified when we release additional videos in this MindMap series, then please subscribe and hit the bell icon to get notifications.
I will provide links to the other MindMap videos in the description below.
Thanks very much for watching! And all the best in your studies


